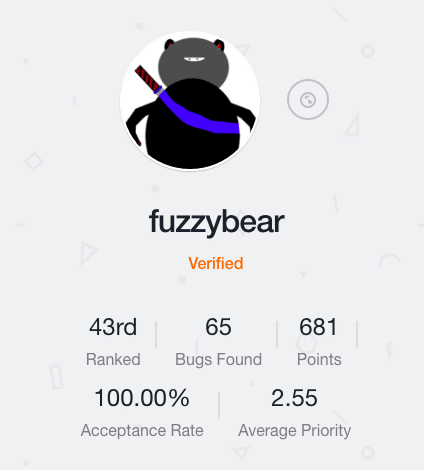
Fuzzybear is #43 on the community leaderboard, with a 100% acceptance rate and an average bug priority of 2.55. In the short time he’s been on Bugcrowd and in bug bounties he has done quite well, successfully finding 65 bugs on Bugcrowd bug bounties, most of which was through private bug bounty programs. He also has one of my favorite usernames in the community!
Read below for our interview with Fuzzybear, where he shares some great practical advice for researchers.
Take us back to your early days, what got you started with technology?
My parents bought a computer and a modem to use for work. I immediately fell in love. I don’t think they got much work done. 😉
How did you get started in security research?
I’ve always had a knack for finding “interesting” things applications do. Usually this was frowned upon, or worse, downplayed and dismissed out of hand.
Now that some companies are really starting to be interested in security and, thanks to Bugcrowd, the barrier to entry as a researcher is low, I decided to throw myself into it and see what I can do.
How long have you been doing bug bounty work?
About a year.
Why do you hack on bug bounties?
1. It’s fun.
2. For the experience and learnings from attacking real targets.
3. The money doesn’t hurt :).
Do you have a specific security focus or specialty that you tend to spend your time on?
Right now I mainly focus on web stuff, but I am learning/trying my hand at binary analysis and mobile. Come on iOS jailbreak!
What motivates you to do what you do? What keeps you going?
The rush of finding an exploitable vulnerability in a real target. Seeing critical vulnerabilities get fixed. And yes, the money :).
Any tips or suggestions that you would give to other bounty hunters?
1. Keep learning about new classes of vulnerabilities and variations on the ones you know.
2. Look for and find examples of a class of vulnerability manually before doing any automation.
3. Automate as much of the “grunt work” of sending requests/fuzzing/etc as you can but ALWAYS do the analysis yourself.
4. Spend as much time as you can learning what your target is doing and how it is put together.
5. Never ignore that “wait this doesn’t look right” feeling. Keep poking at it!
6. When you find a vulnerability, spend some time playing with it and learn from what you find. There is always something unique about a specific vulnerability that could be useful to know in the future.
Where do you think bug bounties are going in the future?
Thanks to the current popularity and media exposure of bug bounties, I hope consumers will start associating companies who are open about their security and have public bug bounties as being more secure and trustworthy, even when they have security incidents.
This will drive more companies to start bug bounties and allocate more money to their bounty programs, bringing in even more researchers and more media exposure, etc.
I hope the end result of this will be an environment where companies are financially rewarded for consistently working with the security community and being open about what their problems are and what they’re doing to fix them.
Once we break through this shroud of secrecy and stop incentivizing companies to sweep their security incidents under the rug maybe we can finally start to get a handle on this thing.
Where do you hope to be two years from now?
Working for someone doing security stuff :).